The tutorial covers the issue of Superfish adware conducting man-in-the-middle attacks to inject ads into web pages, and provides efficient uninstall tips.
The app called Superfish Visual Search, also referred to as Superfish Visual Discovery, happens to be extensively discussed by security professionals and hardware vendors due to the recent newsmaking story associated with it. Within a specific time frame, the Lenovo consumer laptops were shipped with Superfish pre-installed on them, which caused numerous user experience issues and unambiguous security concerns. The thing is, this program was found to indulge in manipulations with legitimate SSL traffic on computers. In particular, it installs a rogue certificate of its own to the trusted root certification authorities list and replaces SSL certificates as the user visits HTTPS sites. On other words, it pulls off a man-in-the-middle attack. This activity is deployed by the software for the purpose of embedding advertisements into SSL protected web pages as well as other sites the victim goes to.
Aside from hardware bundling, Superfish also exploits other distribution channels to infect computers. An example is packaging with third-party freeware, where the potentially unwanted installer might be obscured via recommended setup options that most users opt into. Basically, the idea of this app is fairly interesting and unique as it provides a way to find images on the Internet that match the one of interest. This approach poses an alternative to the keyword search everyone is more accustomed to. However, the widespread regretful trend of today is to implement commendable ideas through questionable methods. Superfish Visual Search, unfortunately, adds malicious tricks to the mix of its features.
As it has been mentioned, the app under analysis installs a root certificate that overrides the rest of the certificates on the computer. This way, Superfish gets the power over the content on all visited websites to a large extent. Not only that – it also poses an additional risk because the deployed activity can lead to security holes opening up and getting exploited by external actors. Compared to these dangers, the problem of ads popping up on web pages appears to be not that much of an issue. And yet, this is definitely irritating and needs to be addressed by all means. It’s very easy to tell whether this adware is on board: it displays price comparison boxes on random sites. These sponsored sections are labeled “Visual Search results” and “Powered by VisualDiscovery”. If these are showing up as you are surfing the web, immediate action should be taken otherwise you might get hacked by remote criminals.
The fix for the malware scenario in question is a compound procedure which implies bad certificate removal, browser troubleshooting and some additional measures.
Superfish virus automatic removal
All the other adware uninstall methods being worth a try, the cleanup using automatic security software guarantees a proven fix involving little user effort and a trouble-free procedure.
- Download and install the featured security tool and launch an in-depth malware checkup by clicking Start Computer Scan buttonDownload Superfish remover
- When the software returns a list of malicious and potentially unsafe items found on the PC, select Fix Threats in order to have Superfish Visual Discovery infection uninstalled from your machine. An additional virtue of this process is the elimination of other threats that may be active in the background.
Use Control Panel to uninstall Superfish adware
- Go to Control Panel from Windows Start menu. If you are using Windows XP or Windows 8, proceed to Add or Remove Programs. If it’s Windows Vista or Windows 7, Uninstall a program is the right option to click
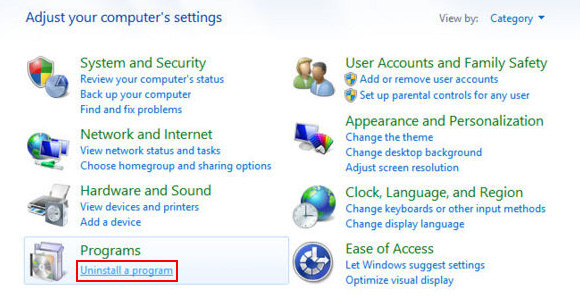
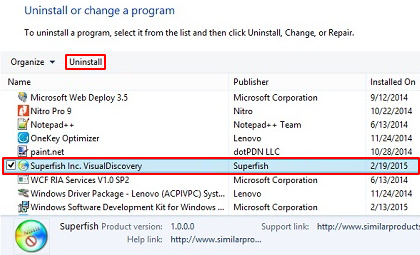
- Carefully examine the list and find the entry for Superfish Visual Discovery there. Once spotted, select the Uninstall/Change option for this item in order to complete the removal
Delete the rogue certificate installed by Superfish
- Сoncurrently press Windows key and R button to open up the Run screen. Type certmgr.msc in there and hit Enter. This will trigger the certificate manager scree
- In the left-hand pane of the interface, select Trusted Root Certification Authorities and click on the Certificates entry
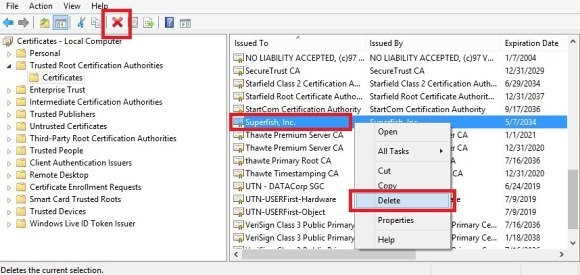
- Find the Superfish certificate on the list, right-click on it and select the Delete option.
Reset the compromised browser to its defaults
Despite the fact that this is a fairly radical fix, resetting the affected web browser is effective. However, be advised you will lose your personalized settings such as temporary Internet files, history, cookies, saved passwords, web form data, toolbars and add-ons. So proceed with caution, and if you’re not sure – perform the cleanup using methods highlighted in the previous sections.
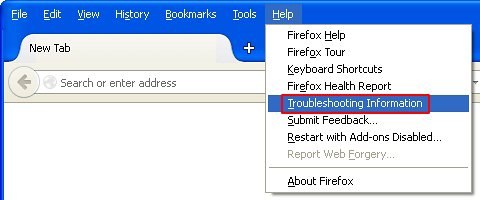
Reset Firefox to its original defaults
- Open Firefox, expand the Help menu on the top of the window, and in the drop-down list pick Troubleshooting Information. Alternatively, simply type in ‘about:support‘ (without quotes) in the Firefox omnibox and hit Enter.
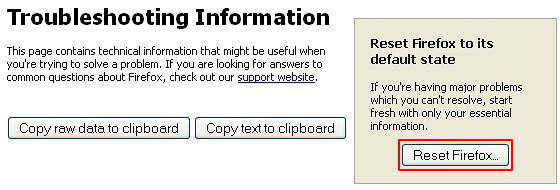
- Troubleshooting Information will open in a separate tab. Click the Reset Firefox button as shown. You’re now done.
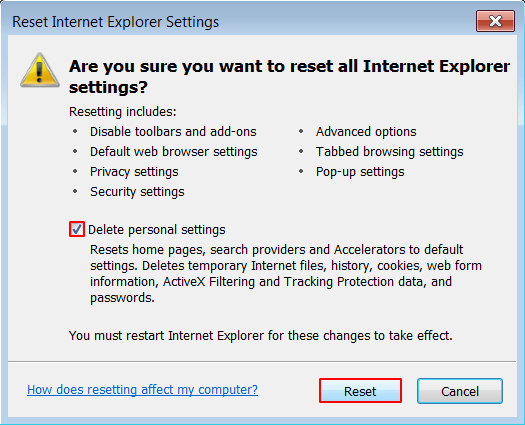
Reset Internet Explorer to its original defaults
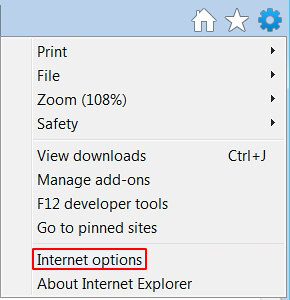
- Launch Internet Explorer and proceed to Tools/Gear icon – Internet Options.
- Select the Advanced tab at the top and click Reset.
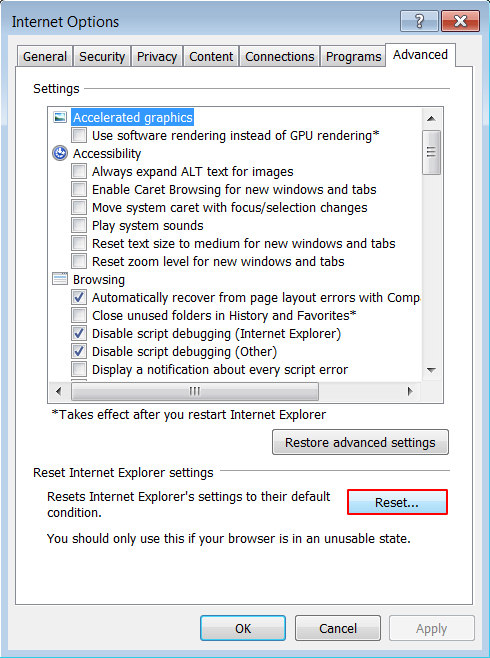
- When IE comes up with the respective screen, read the warning carefully and, if sure, put a checkmark for Delete personal settings. Now click Reset.
Reset Google Chrome to its default values
- Open your Chrome browser, click the Chrome menu icon to the upper right and select Settings on the list. Alternatively, type in ‘chrome://settings‘ (without quotes) in the URL field.
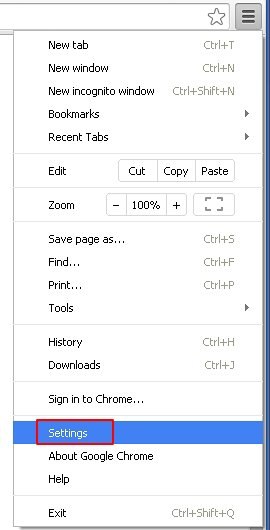
- Find the Show advanced settings… link on the tab that opened up.
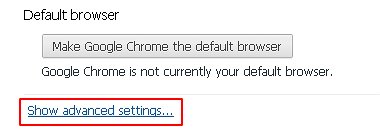
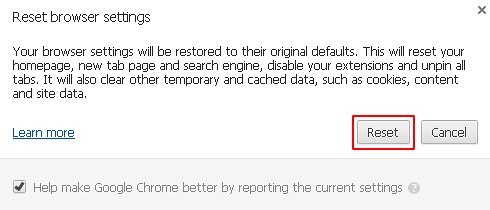
- Under Chrome’s advanced settings, click the button that says Reset browser settings.
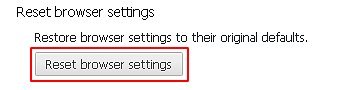
- Be sure to read the information about the personal settings that will be lost if the transaction gets completed. Click Reset if it’s fine with you.
Complete the Superfish removal process
Given the likely persistence of this adware sample, it’s recommended to repeatedly check the machine for its components after the cleanup procedure has been performed. Rescan your system with trusted security suite to make sure Superfish Visual Search extermination has been successful.
Download Superfish free scanner and remover