The post is about malware that sets one’s browser defaults to Bing.vc while skipping the user approval stage, so get rid of it using these instructions. Any software is clearly counterproductive as long as it changes random system settings without consulting the computer’s administrator. In the event these modifications are problematic to reverse, the application …
Aug 10
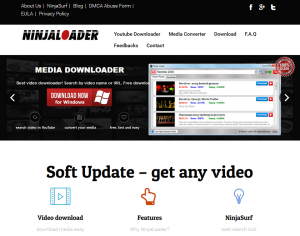
Uninstall Ninja Loader adware from Windows PC
Although Ninja Loader might be of use for downloading audio and movies, it is hard to remove and it displays unwanted ads, so get a method to remove the virus. The authors of Ninja Loader software, on the one hand, state that downloading multimedia content on the Internet doesn’t get any easier with to their …
Aug 05
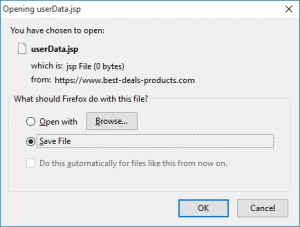
Remove Best-Deals-Products.com malware from Firefox, Chrome and IE
Recurring behind-the-scenes connections to Best-Deals-Products.com during one’s web surfing should be addressed using these malware removal instructions. Some instances of adware assault result in a blatant upshot, where the targeted computer system exhibits apparent abnormality such as configuration-related malfunctioning of web browsers. In these cases, which are prevalent, the victim is bound to visit undesired …
Jul 31
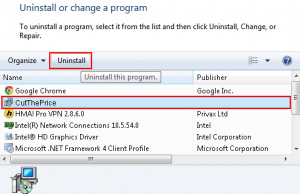
Remove CutThePrice extension (Ads by Cut The Price) from Firefox, Chrome and IE
Use smart instructions to get rid of CutThePrice virus, which is camouflaged inside freeware installs and serves undesired ads to victims after the attack. Finding goods that are dirt cheap is a great many people’s obsession, and the Internet provides fantastic opportunities to make it come true. What’s popular is also a potentially exploitable environment …
Jul 28
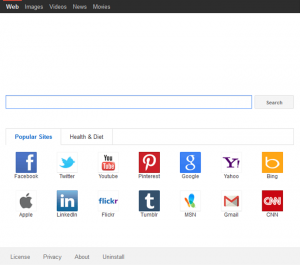
Remove your-home-page.net from Firefox, Chrome and Internet Explorer
The encounter where your-home-page.net becomes one’s default start page and search provider should be treated as malware activity, hence removal is a must. In virus analysis terms, it’s important to differentiate between the symptoms and the objects originally causing them. The users who are getting constantly and forcibly redirected to your-home-page.net while online tend to …
Jul 27
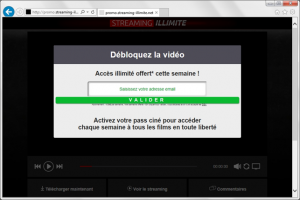
Remove Totaladperformance.com popup virus from Firefox, Chrome and IE
Permanently occurring totaladperformance.com popups are a call for action as they mean there’s adware inside the PC, so get rid of it using this knowledgebase. It takes very little to catch malicious software. In the case of Totaladperformance virus, just a momentary distraction from the installation workflow of a supposedly secure free program is sufficient …
Jul 22
Remove Wander Burst virus ads from Firefox, Chrome and IE
Ads by Wander Burst get users frustrated because they inundate every accessed web page, so adhere to the instructions to uninstall the uninvited application. As convenient as online shopping generally is, the way it is implemented these days tends to get questionable, mostly because there are big moneymaking opportunities involved. While some services have got …
Jul 17
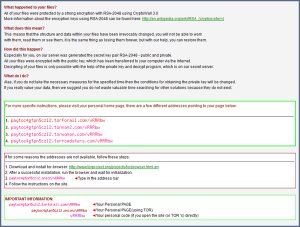
Remove CryptoWall ransomware and decrypt abducted files in Windows
The impact caused by CryptoWall virus, which encrypts one’s data and holds it hostage while extorting a ransom, can be reversed using these instructions. The malicious software to be dissected in this entry was once believed to have gone extinct, but the disappointment and fuss about it came back as its version 3.0 emerged back …
Jul 16
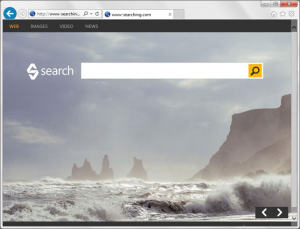
Remove www-searching.com redirect virus from Firefox, Chrome and IE
Although www-searching.com site looks appealing, it is actually a part of adware con, so the related virus should be avoided and eradicated if it’s on a PC. Some adware assaults are quite ordinary and forthright, involving a malicious web browser extension programmed to repeatedly reroute traffic to a single landing page. Others tend to be …
Jul 13
Remove Search Protect virus from Firefox, Chrome and IE
Get the hang of computer troubleshooting with regard to the Search Protect by Conduit malware and act wisely further on to stay away from infections like that. It’s not beyond the realms of possibility that even security-savvy and generally prudent PC users may get tricked into installing a piece of malicious software when surfing the …