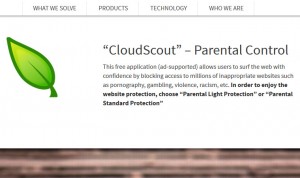
Find out about the adverse influence of the CloudScout Parental Control application, including the nagging issue of ads being displayed on websites. Free software and the term “ad-supported” appear to be adjacent components of a complex whole. On the one hand, this cooperation makes it possible for the developers of open source programs to stay …
April 2015 archive
Apr 23
Remove Ads by Miss Sunshine from Firefox, Chrome and Internet Explorer
Immensely irritating ads displayed by Miss Sunshine add-on can be easily removed using the instructions included in this article along with adware description. Ironically, the piece of software that generates Ads by Miss Sunshine is very likely to make one’s computing ‘weather’ gloomy. Setting figurative expressions aside, this program is not welcome on a PC …
Apr 17
Remove adultube.info popup malware from Firefox, Chrome and IE
A workaround to get rid of nagging popups and web browser redirects to adultube.info site is the number one subject highlighted in this post. When a computer virus executes some harmful code in the background of the compromised system, it’s probably not as frustrating a situation as an X-rated site being triggered off and on …
Apr 06
Remove Ads by Name virus (luu.lightquartrate.com) from Chrome, Firefox and IE
This post comprehensively describes the malware problem of Ads by Name popping up during one’s browsing and provides instructions to solve the issue. As far as online advertising is concerned, it’s a mixed blessing. On the one hand, that’s a fundamental thing that keeps lots of Internet services afloat and actually provides end users with …
Apr 03
Remove Fix My PC aka A1 PC Cleaner rogue software
Learn the grounds for flagging the Fix My PC utility as a fake system optimizer and follow the instructions to remove this hoax from attacked computer. There are PC programs out there which mimic certain features rather than provide the genuine declared functionality. The underground malware industry indulging in this type of misdemeanor is nearly …