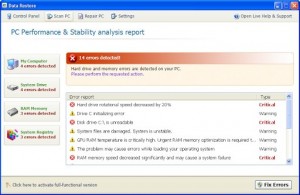
Data Restore, a rogue of the FakeSysDef Family which uses fake scareware of having hard drive and system errors to scare those infected to buy the rogue.
The FakeSysDef rogues also includes an MBR (Master Boot Record) Rootkit like TDSS, TDL#, or Sinowal used for profiting from search engine results hijackings even after the user purchases the rogue.
Files and Locations:
%LOCAL_APPDATA%\<Random File Names>.exe
Note: %LOCAL_APPDATA% refers to:
For XP OS
<drive>:\Documents and Settings\<user>\Local Settings\Application Data
For Vista/Win 7 OS’s:
<Drive>:\Users\<User>\AppData\Local
The DataRestore Rogue can be removed with manual methods, however, as this rogue also includes Master Boot Record Rootkit infections, it is recommend to use our Malware Removal tool, VIPRE Antivirus.
You can download a free trial to remove the rogues of the rogues of the FakeSysDef family from your PC for no cost by clicking on the link below:
http://www.vipreantivirus.com/Antivirus-Trial/VIPRE-Antivirus
If you are unable to download and install our malware removal tool because this has infected your computer and is not allowing you to install the program, you can use our VIPRE Rescue Disc here: